How to Prevent Users From Changing Permissions and Reading Permissions Using Icacls
Y'all tin can use the built-in iCACLS tool to manage NTFS permissions on Windows. The icacls.exe command line tool allows you to go or change Access Control Lists (ACLs) for files and folders on the NTFS file system. In this commodity, we'll look at useful commands for managing NTFS permissions on Windows with iCACLS.
Contents:
- Using iCACLS to View and Set File and Folder Permissions
- How to Backup (Consign) Folder NTFS Permissions?
- How to Restore NTFS Permissions with iCacls?
- Resetting NTFS Permissions to Defaults
- Copying NTFS Permissions from One Folder to Some other
Using iCACLS to View and Fix File and Binder Permissions
The current access permissions to whatsoever object on an NTFS volume can be displayed as follows:
icacls 'C:\Share\Veteran\'
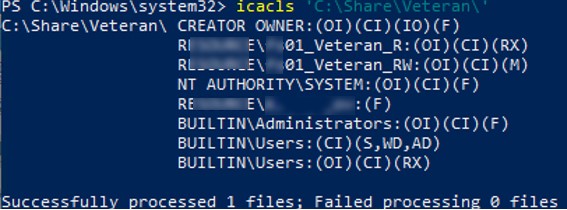
The control will return a list of users and groups that have been assigned access permissions. Permissions are specified using abbreviations:
- F – full admission
- M – change access
- RX – read and execute admission
- R – read-only access
- W –write-only access
- D – delete
Inheritance rights are specified earlier access permissions (inheritance permissions are practical only to folders):
- (OI) – object inherit
- (CI) – container inherit
- (IO) – inherit only
- (I) – inheriting permissions from parent container
With icacls you can change folder permissions.
To grant the "resources\mun-fs01_Auditors" group read and execute (RX) permissions on the folder:
icacls 'C:\Share\Veteran\' /grant resources\mun-fs01_Auditors:RX
To remove a group from a directory ACL:
icacls 'C:\Share\Veteran\' /remove resource\mun-fs01_Auditors
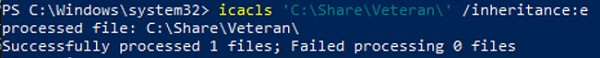
With icacls you tin can enable NTFS permissions inheritance from the parent folder:
icacls 'C:\Share\Veteran\' /inheritance:east
Or disable inheritance with removing all inherited ACEs:
icacls 'C:\Share\Veteran\' /inheritance:r
You tin utilize the icacls.exe to modify buying of a file or folder
icacls 'C:\Share\Veteran\' /setowner resource\j.smith /T /C /L /Q
How to Backup (Consign) Folder NTFS Permissions?
Earlier making significant changes to permissions (move, update ACLs, migrate resources) on an NTFS folder (or shared network folder), information technology is advisable to back upwards the one-time permissions. This re-create will allow you to render to the original settings, or at to the lowest degree clarify the old permissions for a specific file/directory.
Y'all can utilize the icacls.exe tool to export/import current NTFS directory permissions. To get all ACLs for a specific folder (including sub-directories and files), and export them to a text file, run the post-obit command:
icacls grand:\veteran /salve c:\backup\veteran_ntfs_perms.txt /t /c
Note. /t fundamental is used to get ACLs for all subdirectories and files, /c allows to ignore admission errors. By adding /q selection, you can disable the brandish of data about successful admission to the file organisation objects.
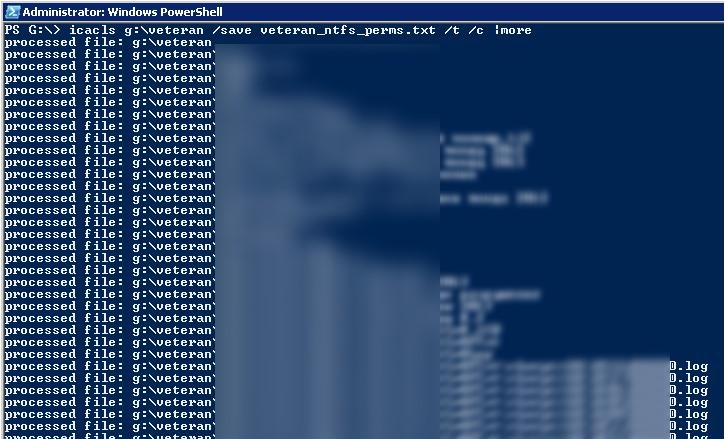
Depending on the number of files and folders, the consign of permissions can take quite a long time. After the control has been executed, the statistics on the number of successful or failed processing of files will exist displayed.
Successfully processed 3001 files; Failed processing 0 files
Open the file veteran_ntfs_perms.txt using any text editor. As you tin can run across, information technology contains the total list of files and folders in a directory, and each particular has the electric current permissions specified in SDDL (Security Descriptor Definition Language) format.
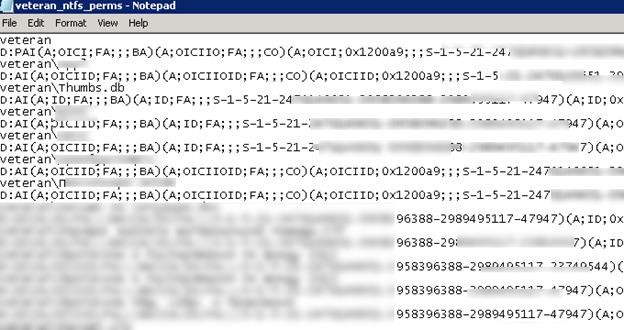
For case, the current NTFS permissions for the folder root are as follows:
D:PAI(A;OICI;FA;;;BA)(A;OICIIO;FA;;;CO)(A;OICI;0x1200a9;;;South-1-5-21-2340243621-32346796122-2349433313-23777994)(A;OICI;0x1301bf;;;S-ane-5-21-2340243621-32346796122-2349433313-23777993)(A;OICI;FA;;;SY)(A;OICI;FA;;;S-1-5-21-2340243621-32346796122-2349433313-24109193)S:AI
This string describes the access for some groups or users. We won't consider SDDL syntax in particular (the SDDL format was briefly discussed in the article "How to View and Modify Service Permissions in Windows?"). Let'south focus on a small piece of SDDL by selecting just i object:
(A;OICI;FA;;;South-1-5-21-2340243621-32346796122-2349433313-24109193)
A – access type (Permit)
OICI – inheritance flag (OBJECT INHERIT+ CONTAINER INHERIT)
FA – permission type (SDDL_FILE_ALL – all allowed)
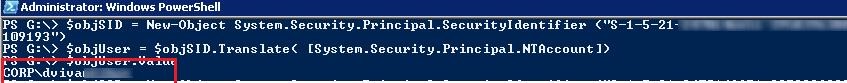
S-ane-five-21-2340243621-32346796122-2349433313-24109193 – SID of the account or domain group for which the permissions are set. To convert SID to the business relationship or group proper name, utilise the post-obit PowerShell command:
$objSID = New-Object System.Security.Principal.SecurityIdentifier ("South-1-five-21-2340243621-32346796122-2349433313-24109193")
$objUser = $objSID.Translate( [System.Security.Principal.NTAccount])
$objUser.Value
Or use one of the commands:
Get-ADUser -Identity SID
or
Get-ADGroup -Identity SID
Thus, yous take found that the user corp\dvivar had Full Command permissions on this directory.
How to Restore NTFS Permissions with iCacls?
Yous can restore NTFS permissions on a folder using the previously created veteran_ntfs_perms.txt file. To set NTFS permissions on objects in the directory according to the values in the ACL fill-in file, run this command:
icacls thousand:\ /restore c:\backup\veteran_ntfs_perms.txt /t /c
Note. Please, notation that when importing permissions from the file, yous should specify the path to the parent directory instead of the folder proper name.
After all permissions have been recovered, the statistics on the number of the processed files will too be displayed.
Notation that the backup ACL file contains relative, not absolute, file paths. This means that you can restore permissions on a folder even after moving it to a different drive/directory.
Resetting NTFS Permissions to Defaults
You lot can utilise the icacls tool to reset the binder permissions (also as nested files and sub-directories).
icacls C:\share\veteran /reset /T /Q /C
This control will enable inherited NTFS permissions for the specified object, and volition remove whatsoever other ACLs.
Copying NTFS Permissions from 1 Folder to Another
Y'all tin apply a text file with ACLs backup to copy NTFS permissions from one directory to another.
Get-go, back up NTFS permissions of the source folder:
icacls 'C:\Share\Veteran' /save C:\PS\save_ntfs_perms.txt /c
Then use the saved ACLs to the target binder:
icacls D:\Share /restore C:\PS\save_ntfs_perms.txt /c
This will work if the source and destination folders are named the same. What if the target folder name is different? For case, you need to re-create NTFS permissions to D:\PublicDOCS folder.
The easiest way is to open up the save_ntfs_perms.txt file in notepad and edit the folder name. Use the Replace function to supplant the Veteran name with PublicDOCS.
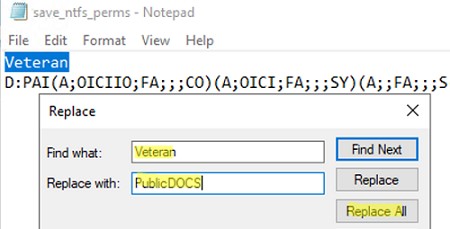
Then import NTFS permissions from the file and employ them to the target folder:
icacls D:\ /restore C:\PS\save_ntfs_perms.txt /c
It's even easier to copy NTFS permissions from ane folder to another using PowerShell:
Get-Acl -Path 'C:\Share\Veteran' | Set-Acl -Path 'E:\PublicDOCS'
Source: http://woshub.com/how-to-backup-and-restore-ntfs-permissions-using-icacls/
Post a Comment for "How to Prevent Users From Changing Permissions and Reading Permissions Using Icacls"